Microsoft Entra (aka Azure AD) Integration
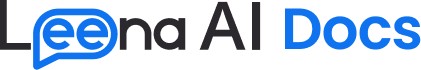
Step 1: Access Microsoft Entra Portal
-
Click on App Registration under Entra ID
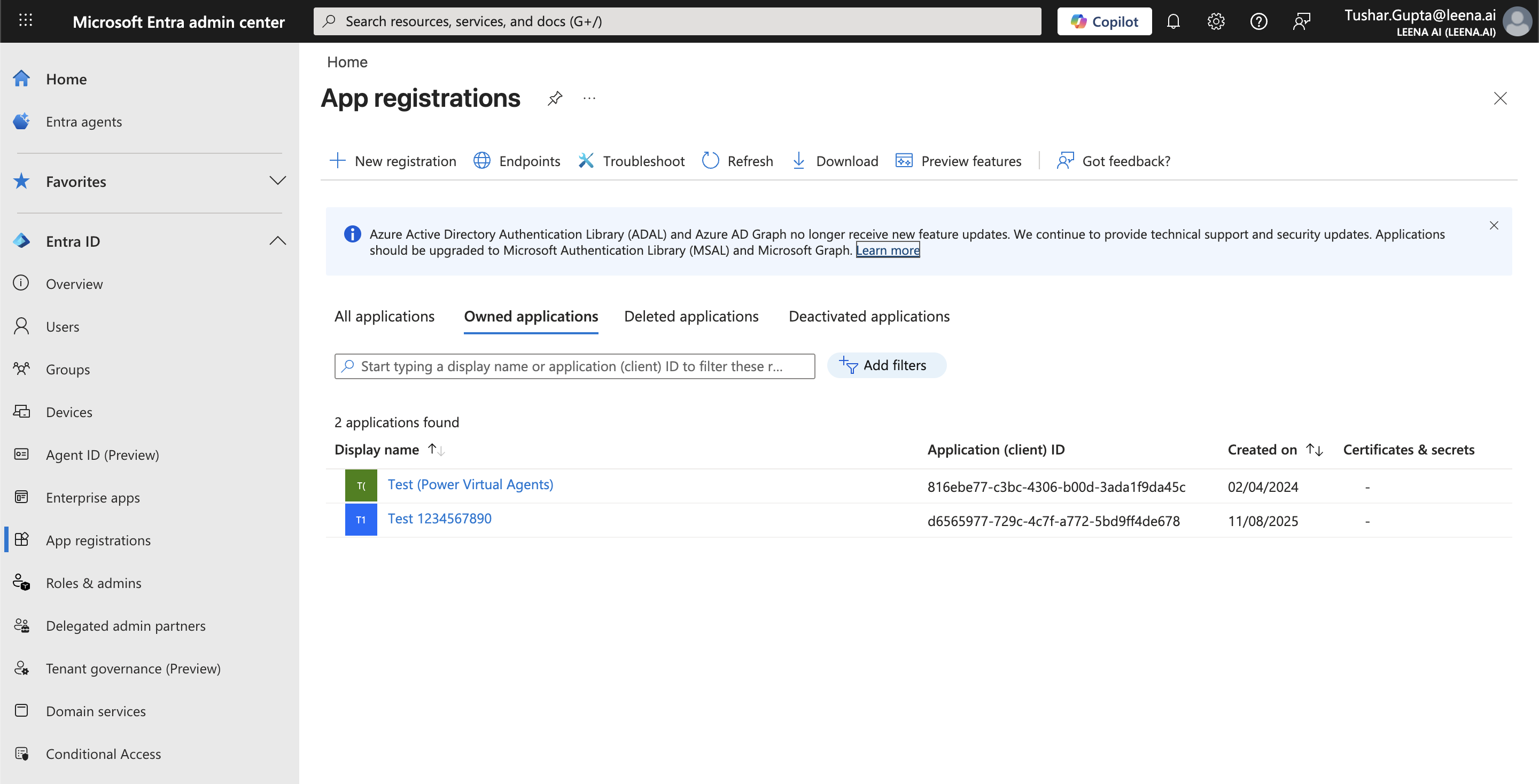
Step 2: Create New Registration
- Click on + New Registration
Step 3: Configure Application
-
Provide a Name for the Application (e.g., "Leena AI Integration")
-
Under Supported account types, select "Single tenant only"
-
Click Register
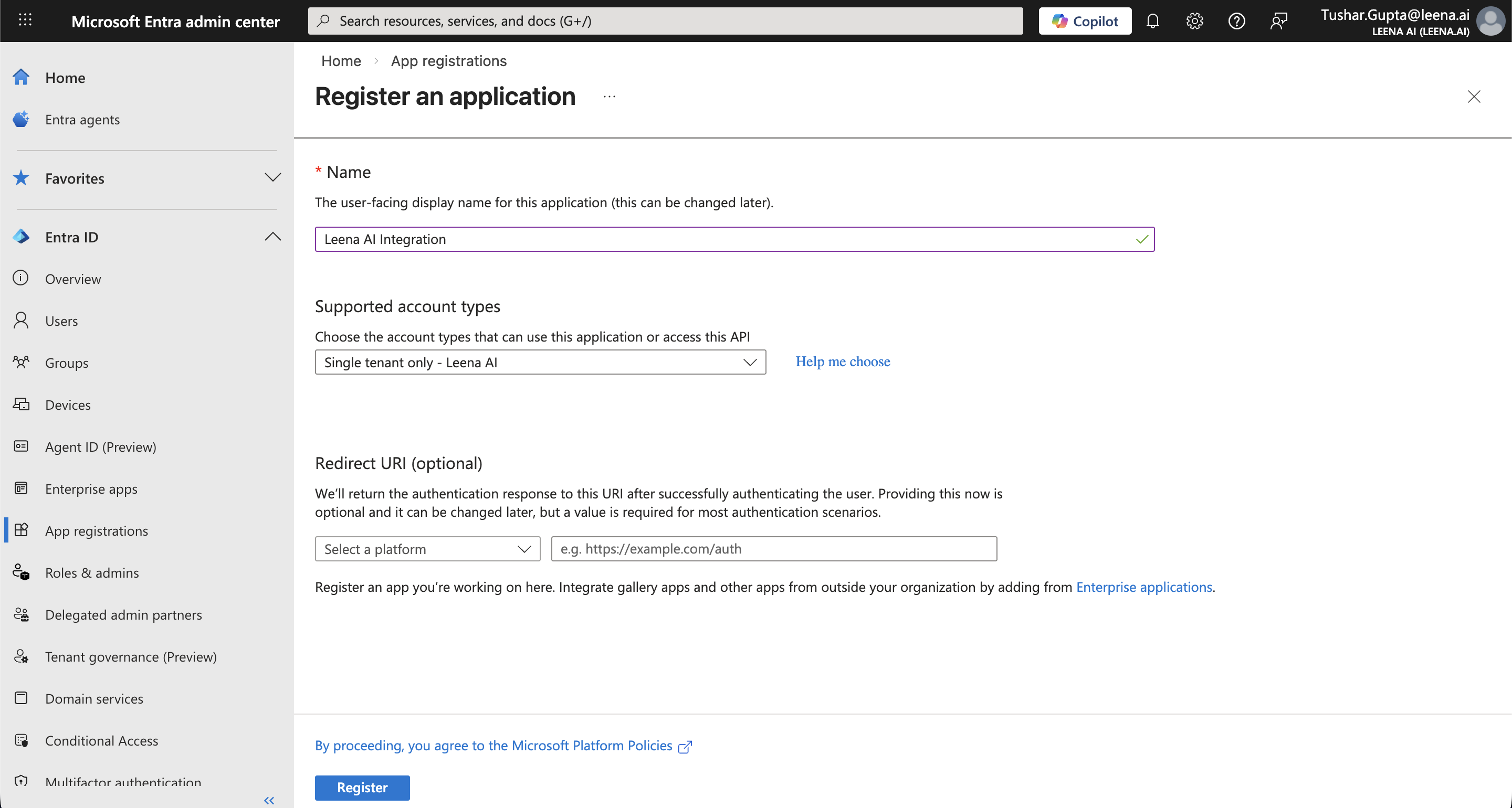
Step 4: Copy Tenant ID and Client ID
-
After registration, you'll be taken to the application Overview page
-
Locate and copy the following values:
- Application (client) ID
- Directory (tenant) ID
-
Share these with Leena AI
Step 5: Create Client Secret
-
In the left navigation menu, click on Certificates & secrets
-
Select the Client secrets tab
-
Click on + New client secret
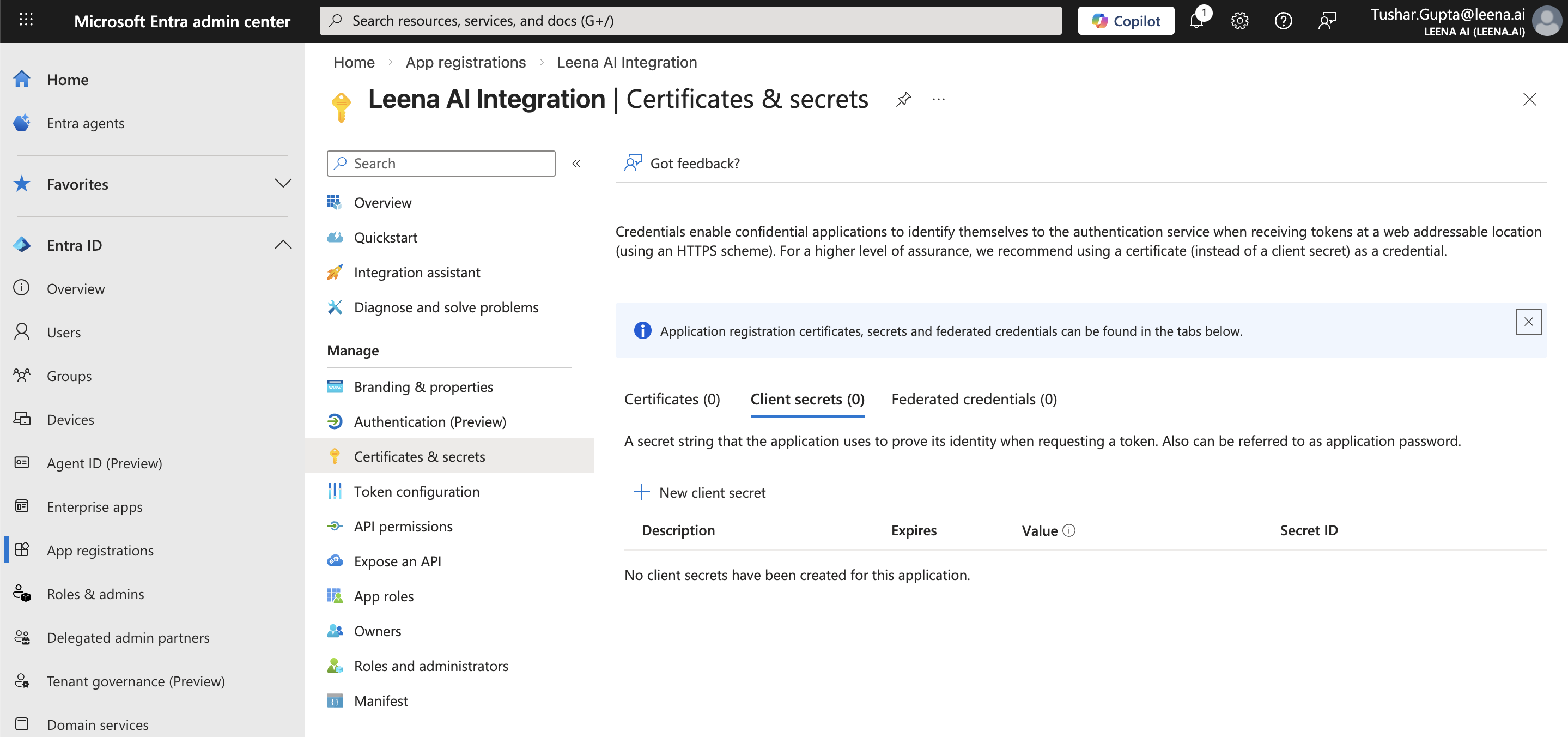
-
In the popup dialog:
- Add a Description (e.g., "Leena AI Secret")
- Set Expires to 24 months
-
Click Add
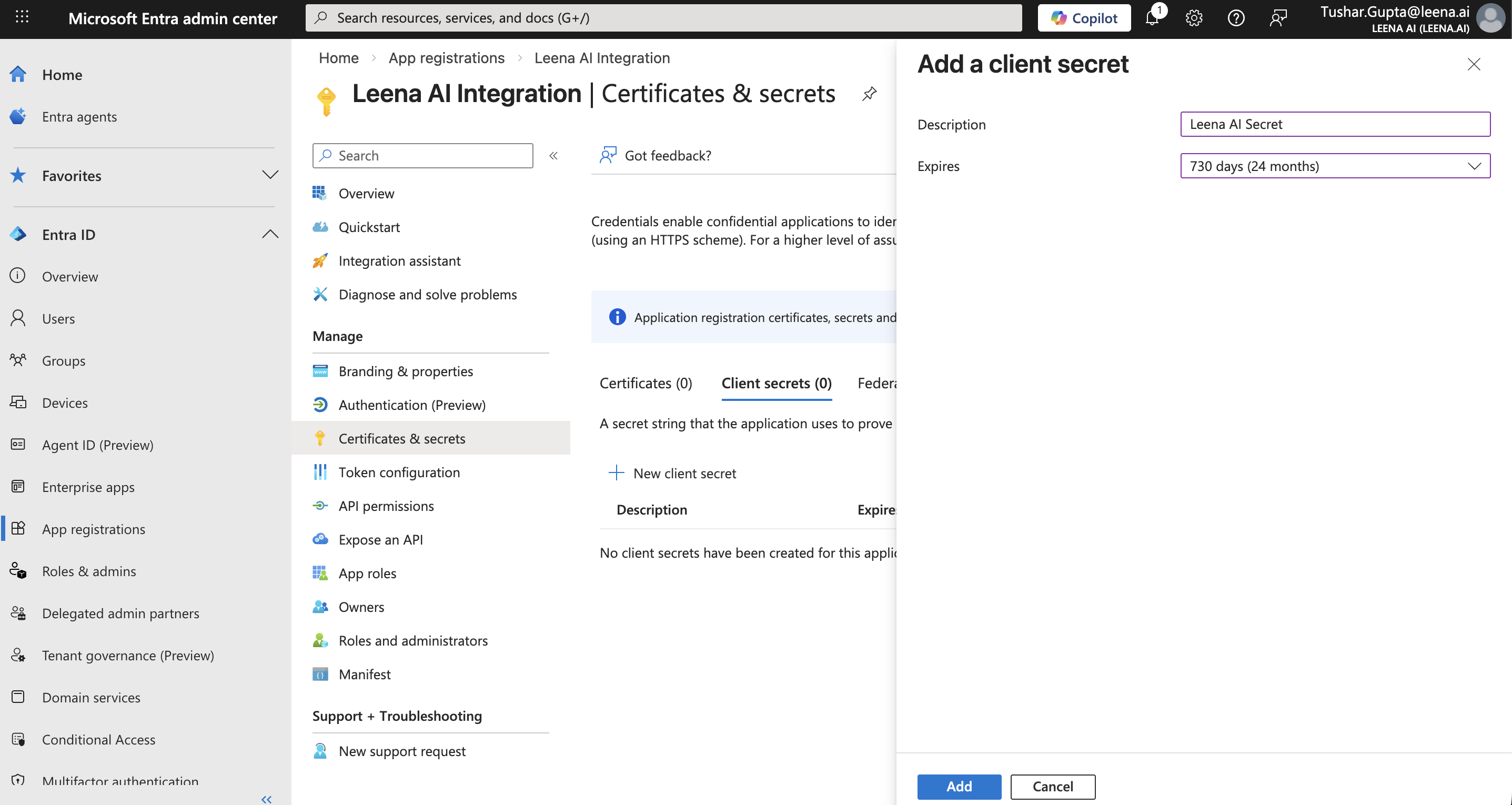
-
Important: Copy the Secret Value immediately (it will only be shown once)
-
Share this secret value securely with Leena AI
Step 6: Configure API Permissions
-
In the left navigation menu, click on API permissions
-
Click + Add a permission
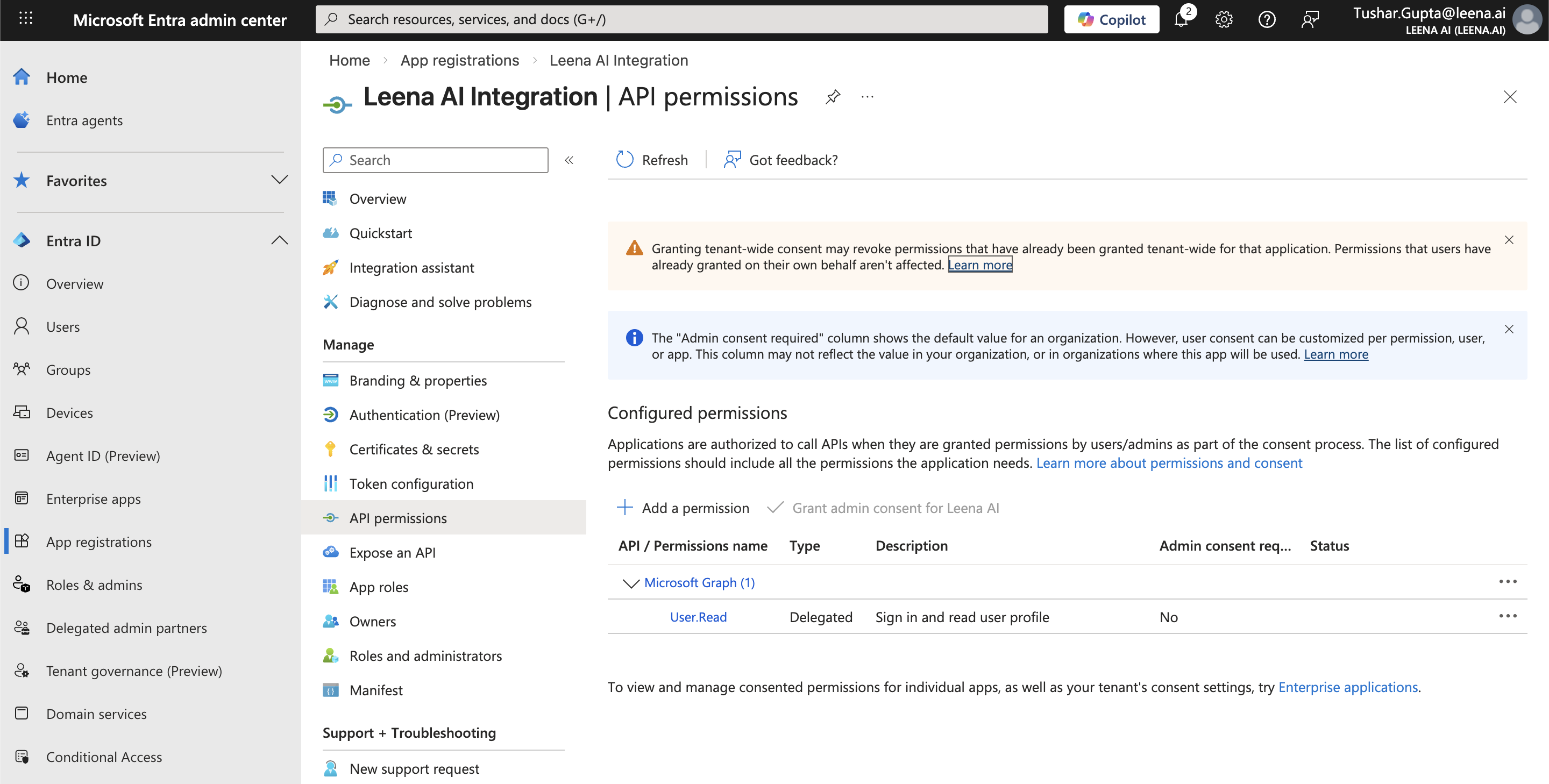
-
Select Microsoft Graph
-
Click Application permissions
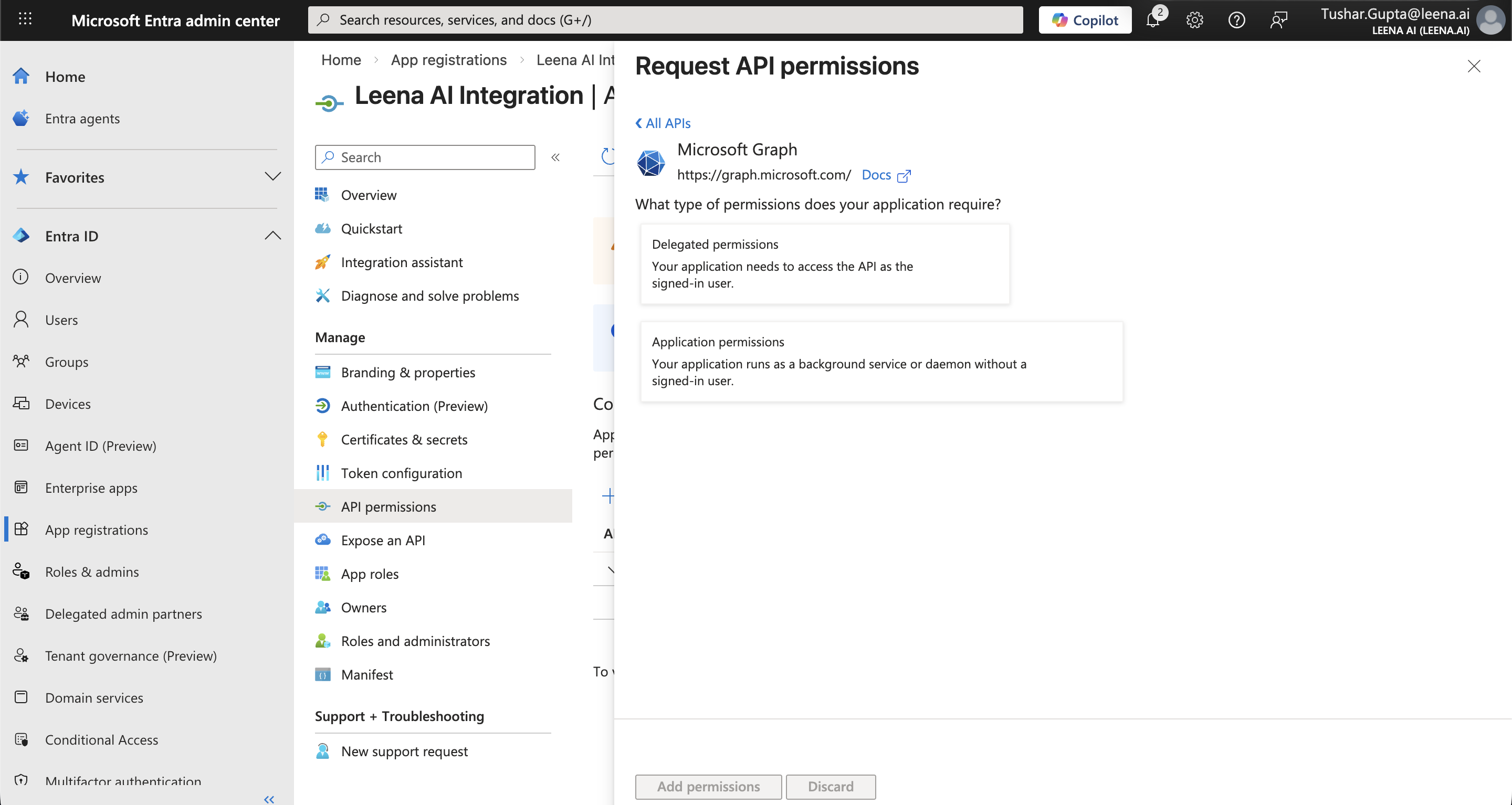
-
Search and select the following:
-
User.Read.All- Read all users' full profiles -
GroupMember.Read.All- Read user profiles within a group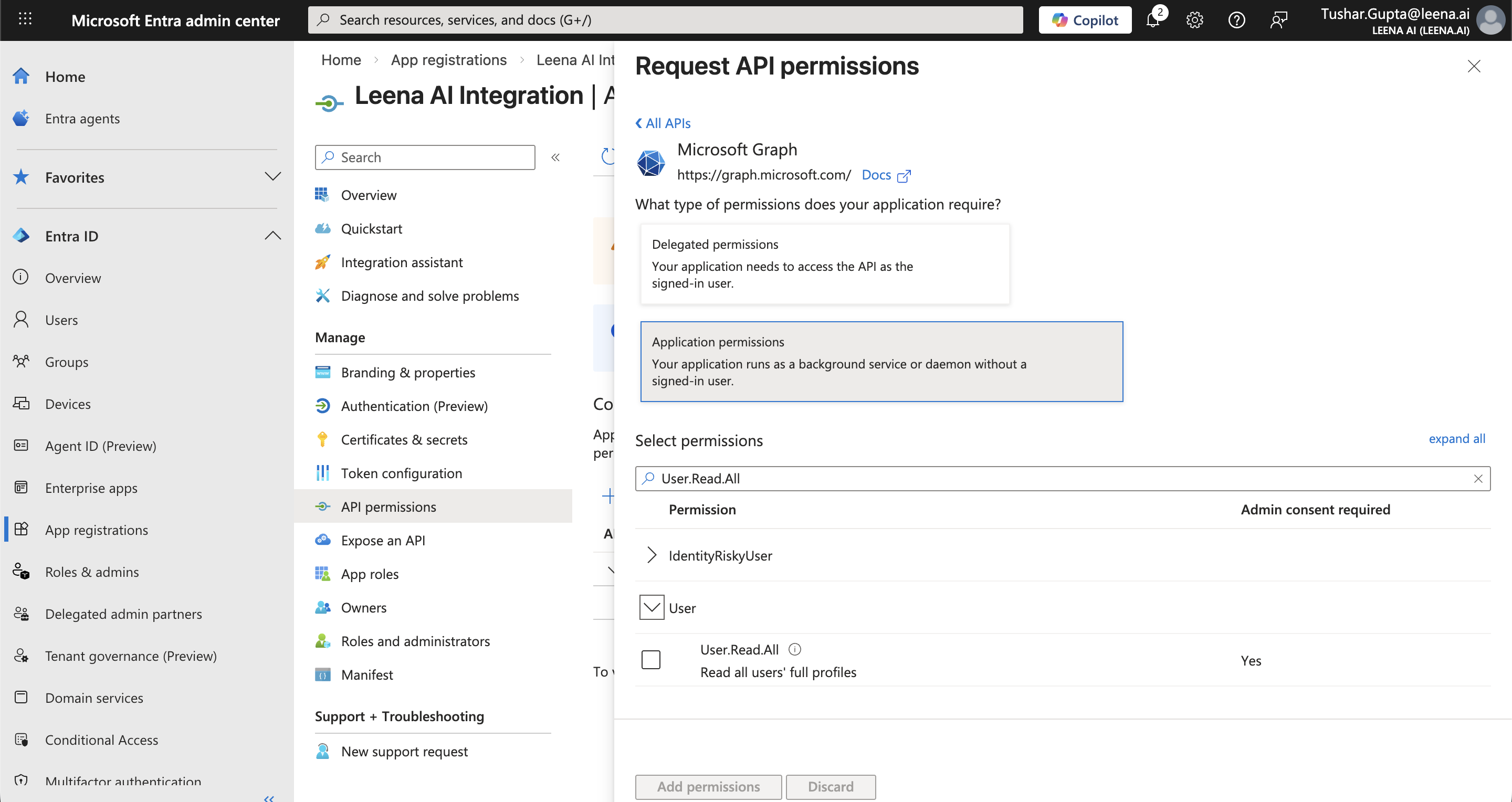
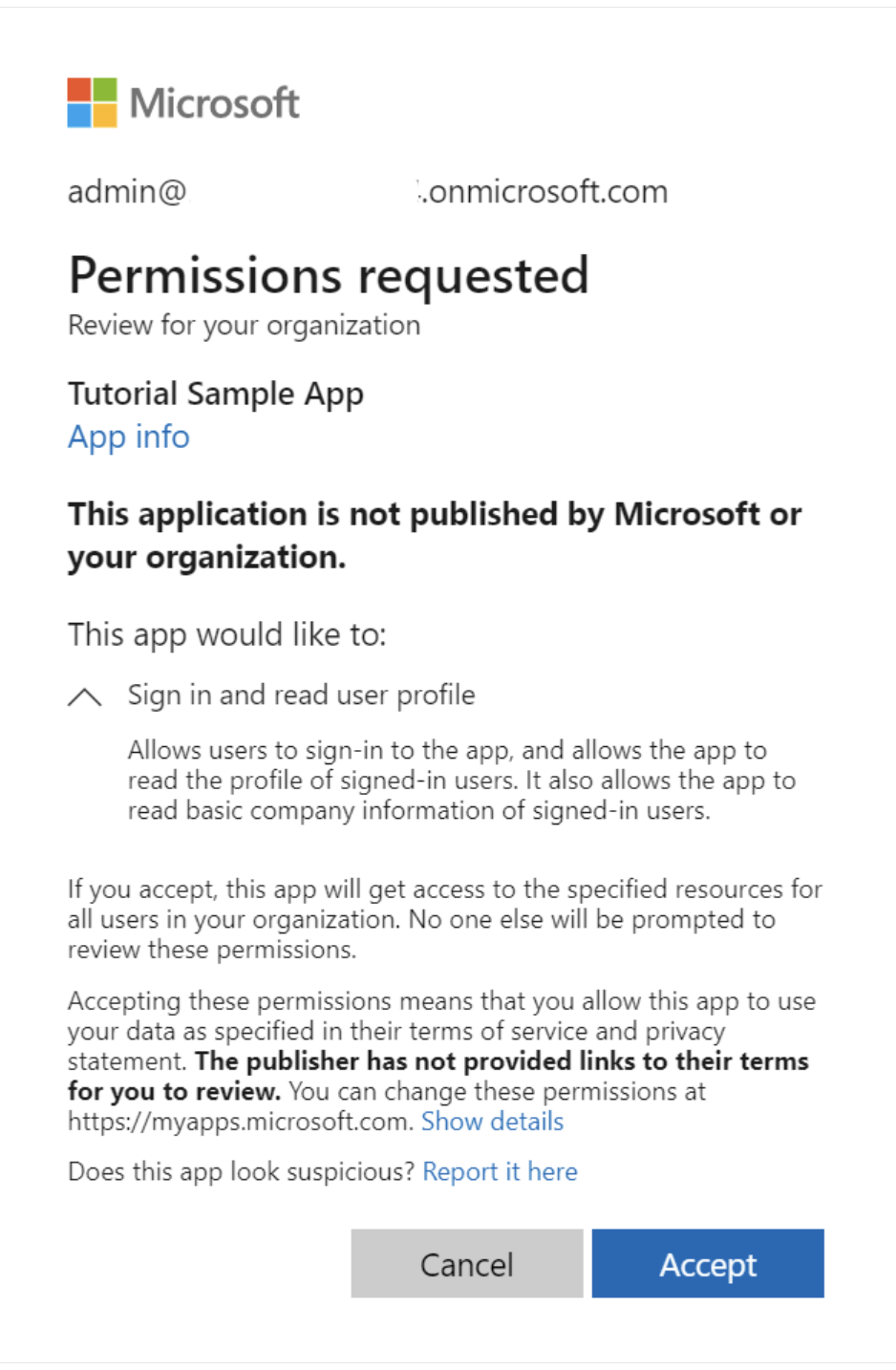
Step 7: Grant Admin Consent
- After adding all permissions, click Grant admin consent for [Your Organization]
- Confirm by clicking Yes
- Verify that all permissions show a green checkmark under "Status"
Step 8: Share Credentials with Leena AI
Please share the following information securely with your Leena AI representative:
| Item | Description | Where to Find |
|---|---|---|
| Tenant ID | Directory (tenant) ID | App Registration → Overview |
| Client ID | Application (client) ID | App Registration → Overview |
| Client Secret | Secret value | Certificates & secrets (copied in Step 5) |
For UAT/Testing (Optional)
If testing with a specific group of users, also provide:
- Group ID: The ID of the Azure AD group containing test members
- Additional Permission: Add
GroupMember.Read.Allunder Application Permissions
Updated 2 months ago